We're aware of a variant of ransomware that has been detected in corporate environments. Threat Name:
Ransom-WannaCry (also known as
WCry,
WanaCrypt,
WannaCrypt, and WanaCrypt0r).
See the related articles below:
Minimum DATs for coverage:
- Endpoint Security (ENS) 2978 or higher *
- VirusScan Enterprise (VSE) 8527 or higher *
* Trellix-defined content protection against known variants.
As a best practice, configure repository update tasks with a minimal refresh interval. This practice makes sure that new content is applied when we release it.
This article is updated as and when additional information is available. Continue to monitor this article for updates.
Topics in this article
Symptoms of infected systems
VSE Access Protection rules
ENS Access Protection rules
ENS Adaptive Threat Protection – Real Protect and Dynamic Application Containment
ENS Dynamic Application Containment rules
Advanced Threat Defense coverage for WannaCry Ransomware
IPS coverage for WannaCry Ransomware
Frequently Asked Questions
Recent updates to this article
Para receber notificações por e-mail quando este artigo for atualizado, clique em Assinar na lateral direita da página. Você deve estar conectado para assinar.
| Date |
Update |
| January 19, 2024 |
Removed category tags for End of Life versions. |
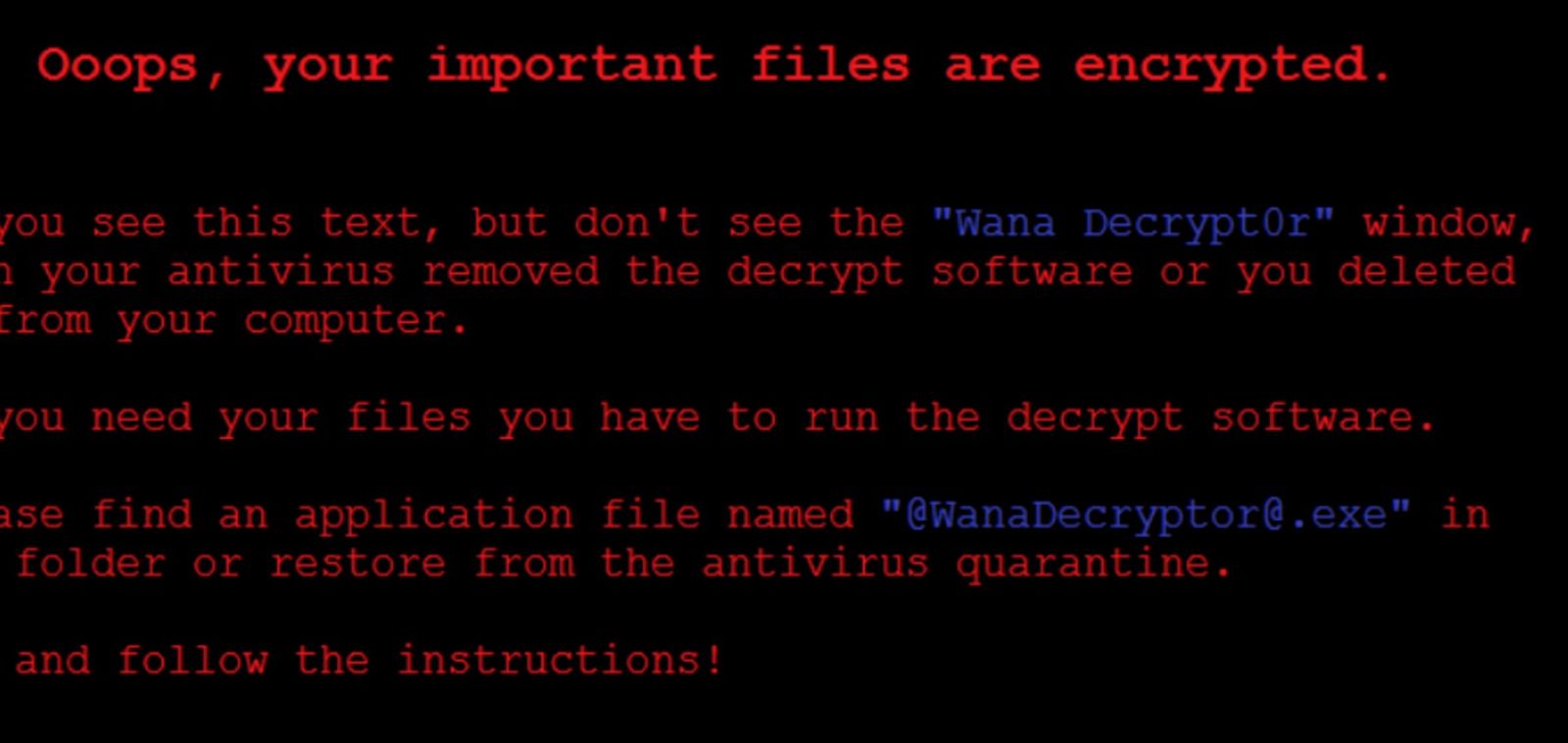
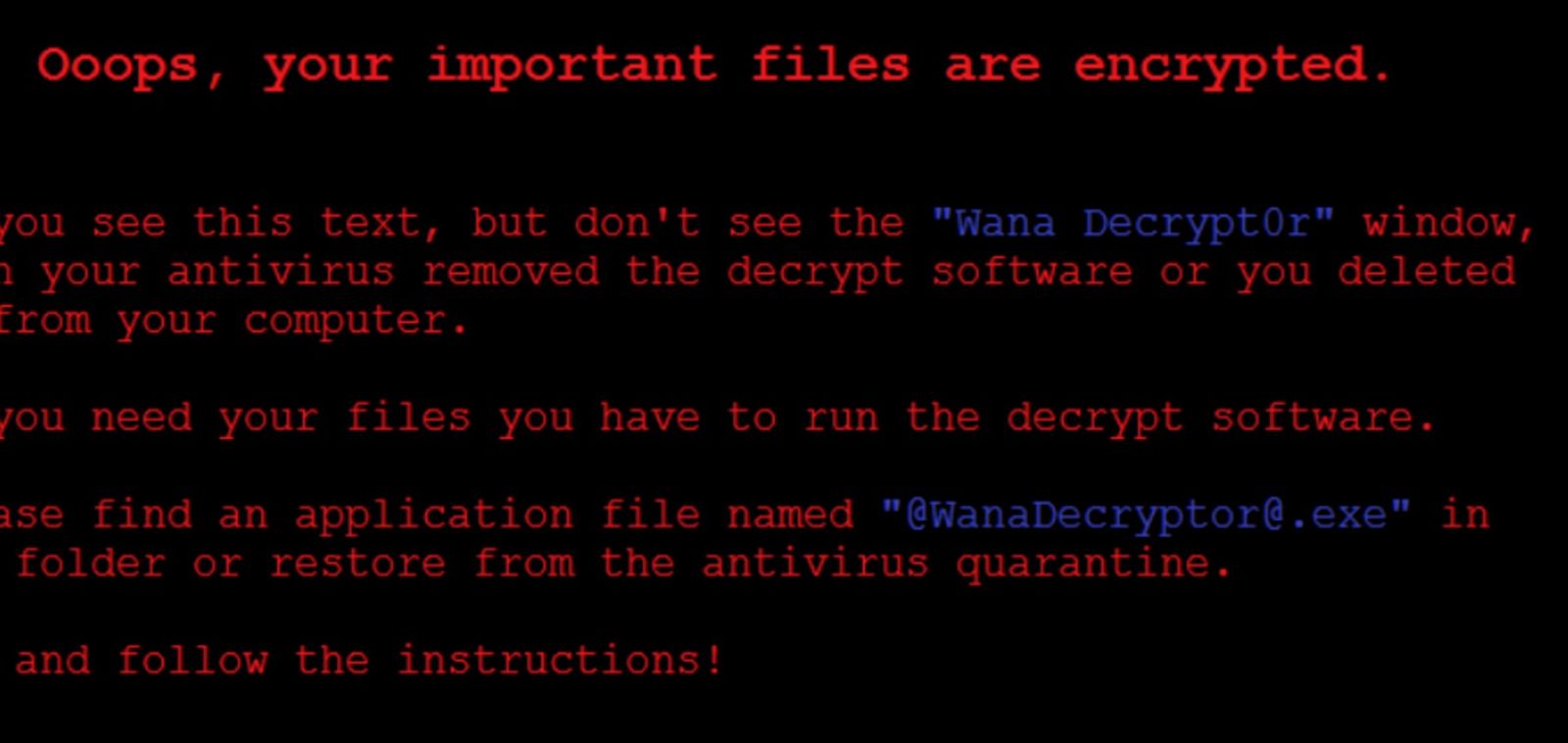
This threat exhibits the following symptoms on infected systems:
- Files are encrypted with the .wnry, .wcry, .wncry, .wcryt, and .wncryt extension. Users see a screen with a ransom message.
- Users see the following Ransom-WannaCry Desktop Background:
- On restarting, impacted systems have a blue screen error and can't start.
- Encryption is seen on the local host and open SMB shares.
IMPORTANT: Immediately install the Critical Microsoft Patch MS17-010 to prevent SMB shares from becoming encrypted. For details, see this Microsoft article.
Back to top
ENS and VSE Access Protection Proactive Measures
| NOTE: The ENS and VSE Access Protection rules prevent creation of the .WNRY file. This rule prevents the encryption routine, which is where you see the encrypted files that contain one or more .WNCRYT, .WNCRY, or .WCRY extensions. By implementing the block against .WNRY, other blocks aren't needed for the encrypted file types. |
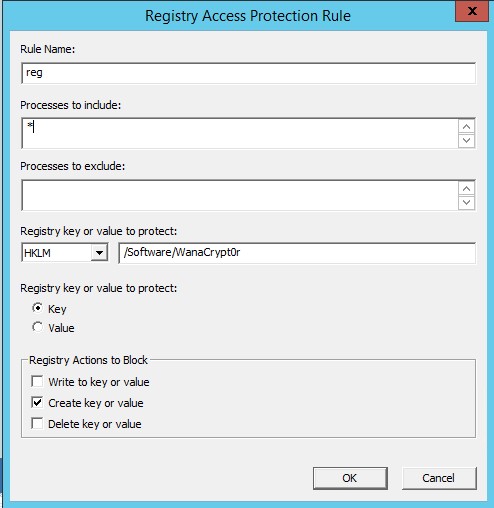
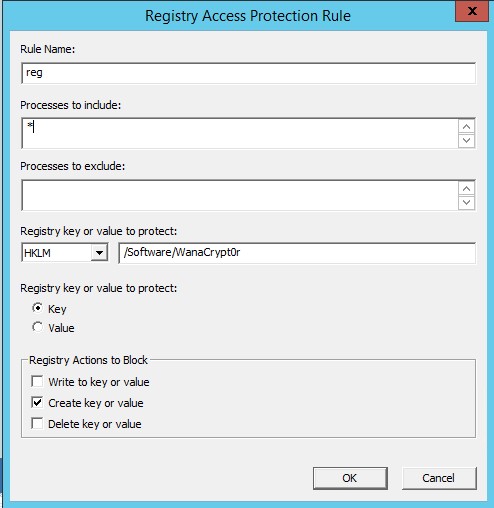
Use VSE Access Protection rules:
Rule 1:
Rule Type: Registry Blocking Rule
Process to include: *
Registry key or value to protect: HKLM - /Software/WanaCrypt0r
Registry key or value p protect: Key
File actions to prevent: Create key or value
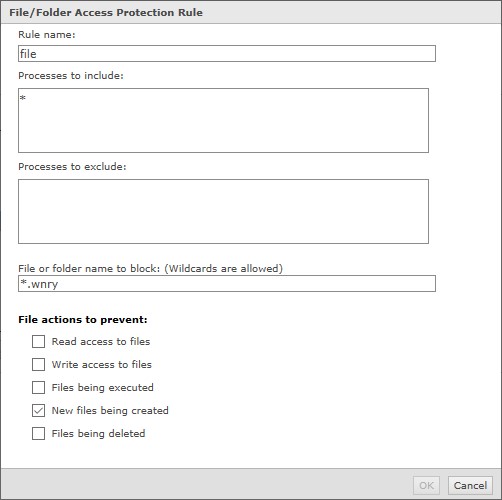
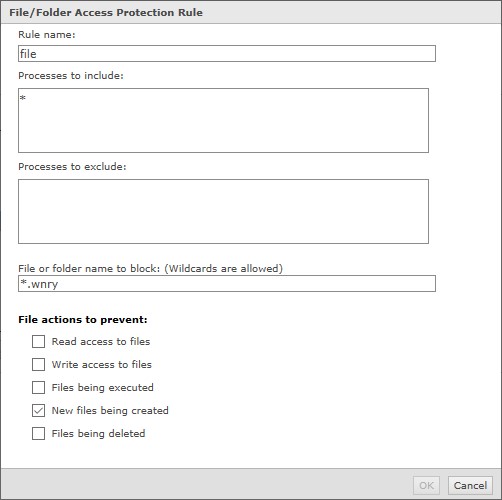
Rule 2:
Rule Type: File/Folder Blocking Rule
Process to include: *
File or folder name to block: *.wnry
File actions to prevent: New files being created
Back to top
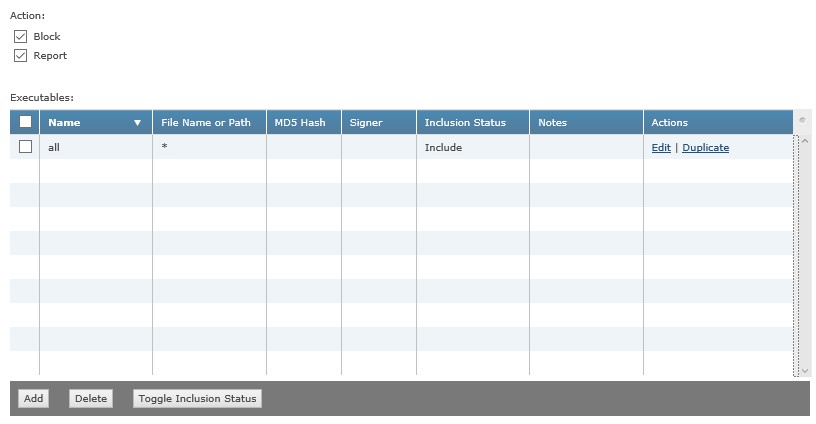
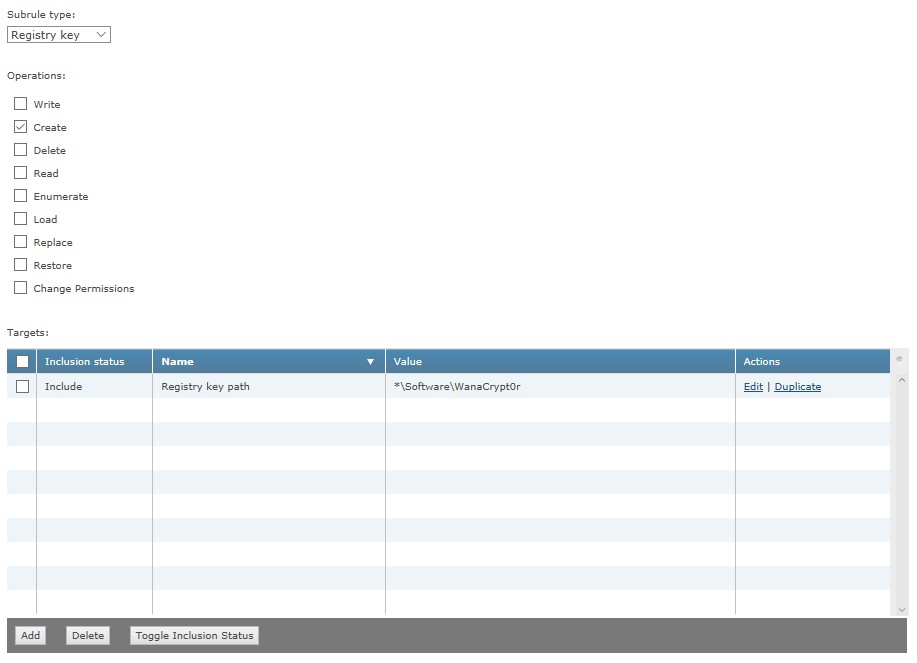
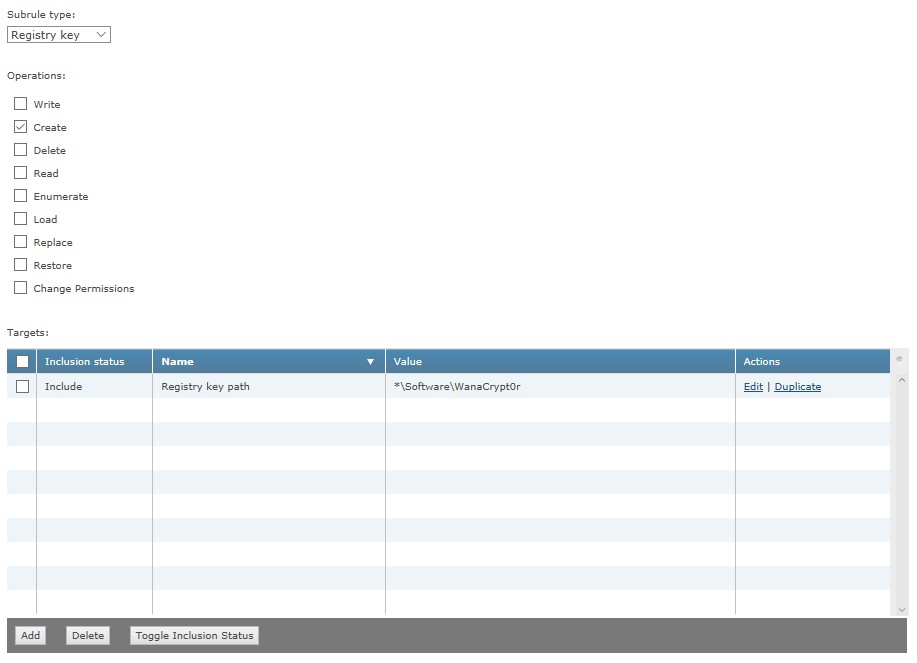
Use ENS Access Protection rules:
Rule 1:
Executable 1:
Inclusion: Include
File Name or Path: *
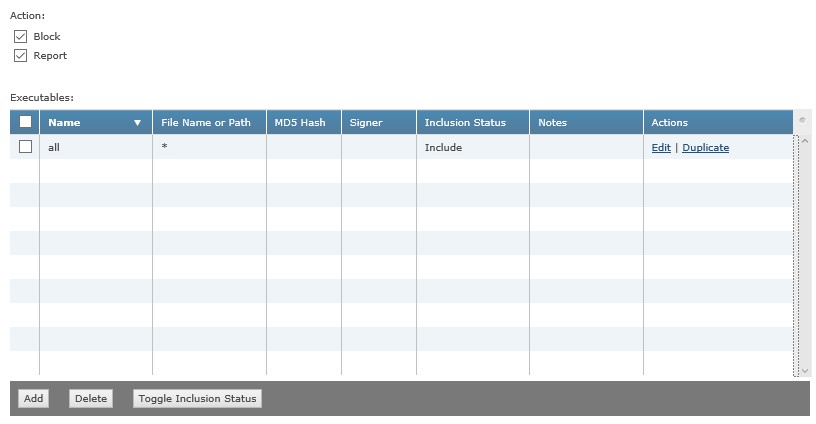
SubRule 1:
SubRule Type: Registry key
Operations: Create
Target 1:
Inclusion: Include
File, folder name, or file path: *\Software\WanaCrypt0r
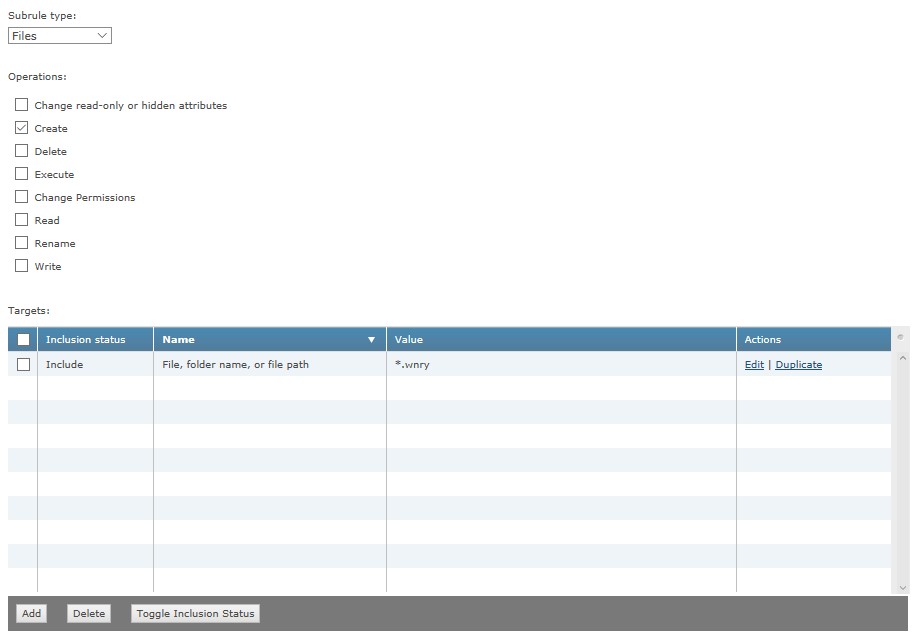
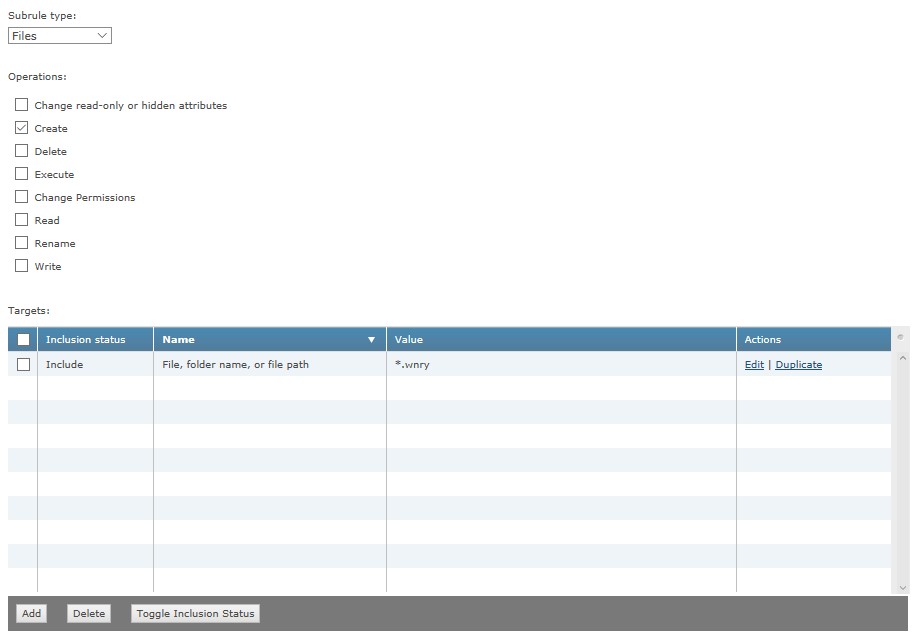
SubRule 2:
SubRule Type: Files
Operations: Create
Target 1:
Inclusion: Include
File, folder name, or file path: *.wnry
Back to top
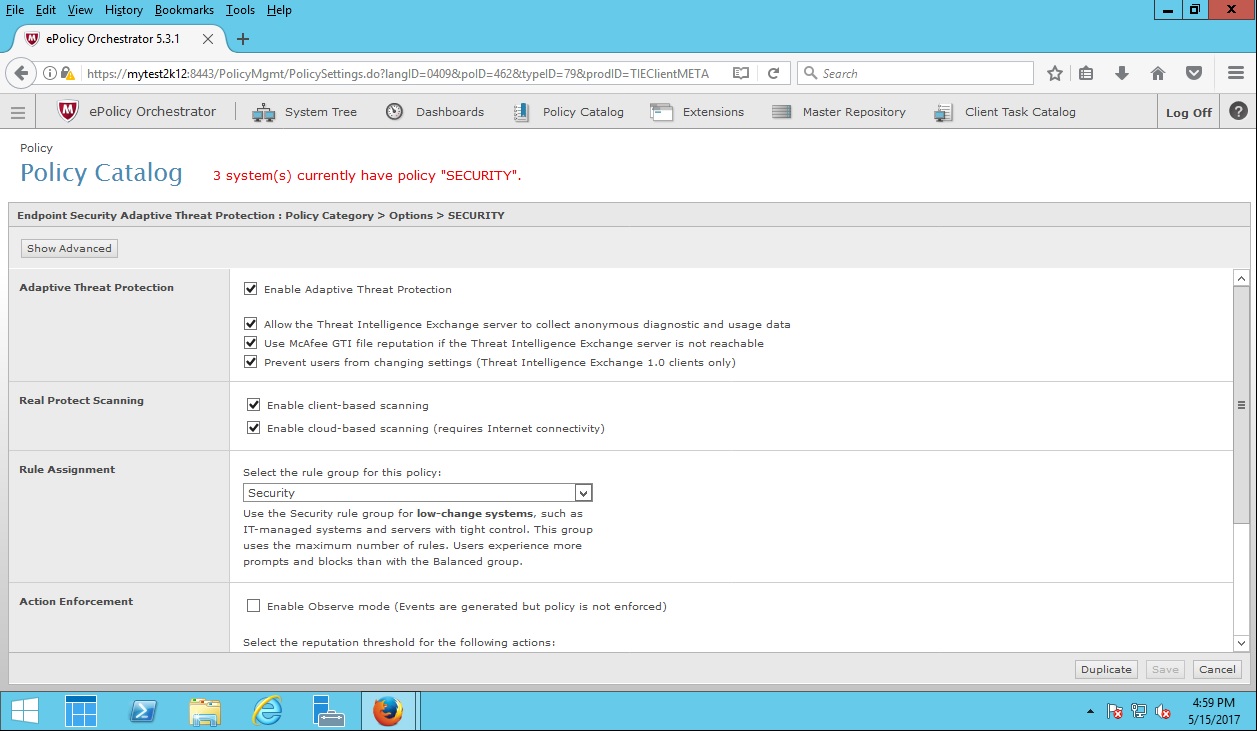
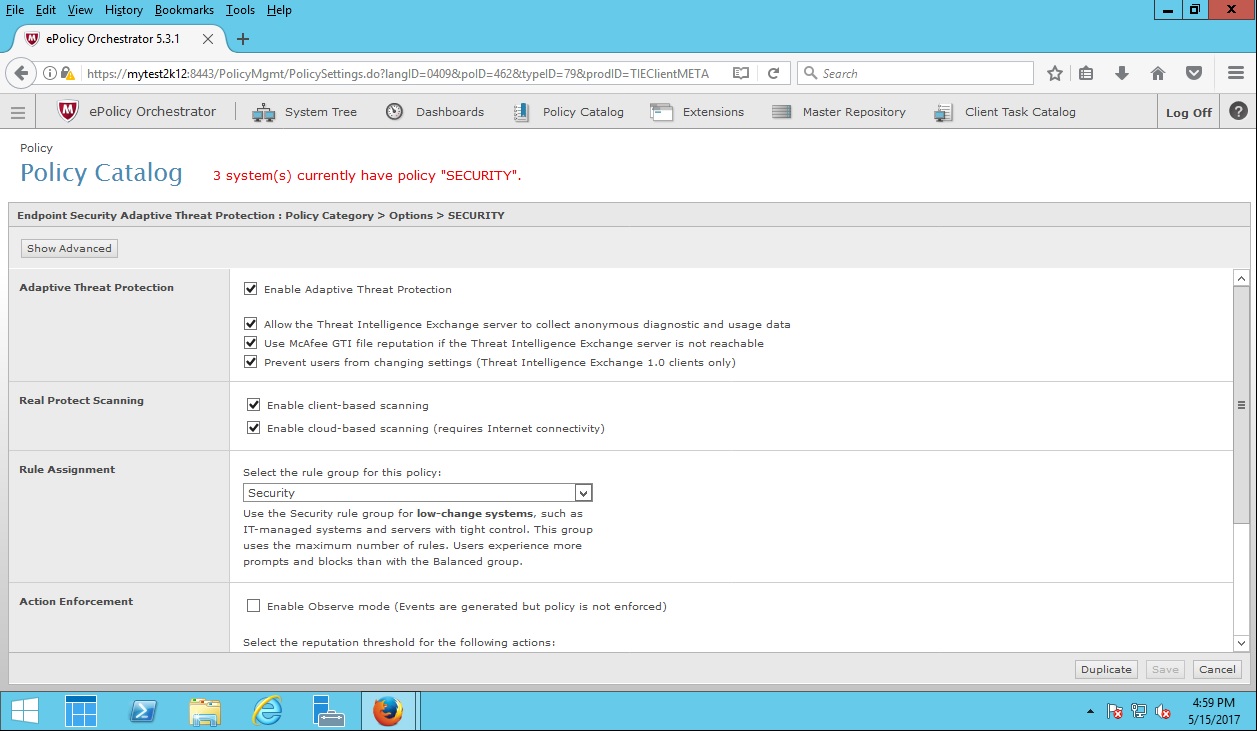
ENS with Adaptive Threat Protection (ATP) – Real Protect and Dynamic Application Containment (DAC)
ENS ATP Real Protect, with DAC, provides next-generation protection against unknown exploits.
ENS ATP provides full protection against all known variants of the WannaCry exploit. We recommend the following ATP configuration for detection of unknown WannaCry variants.
- Configure the following setting in the Adaptive Threat Protection - Options Policy:
Rule Assignment = Security (default setting is Balanced)
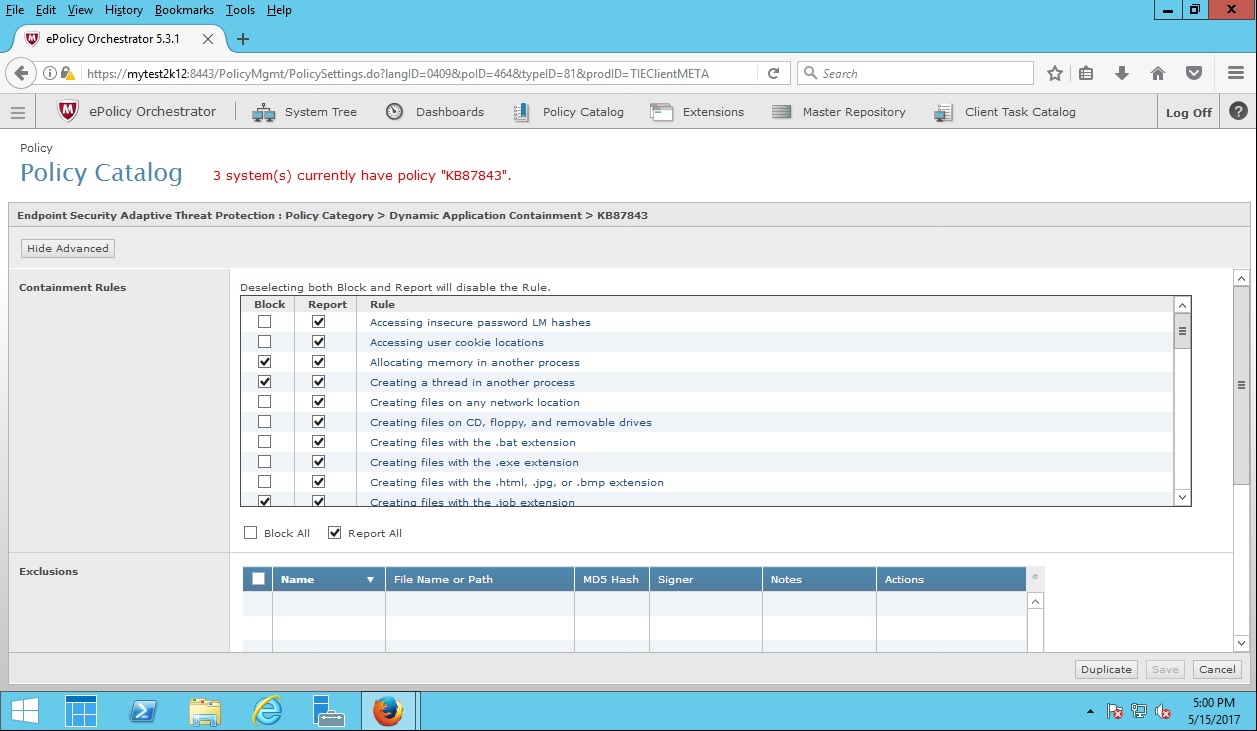
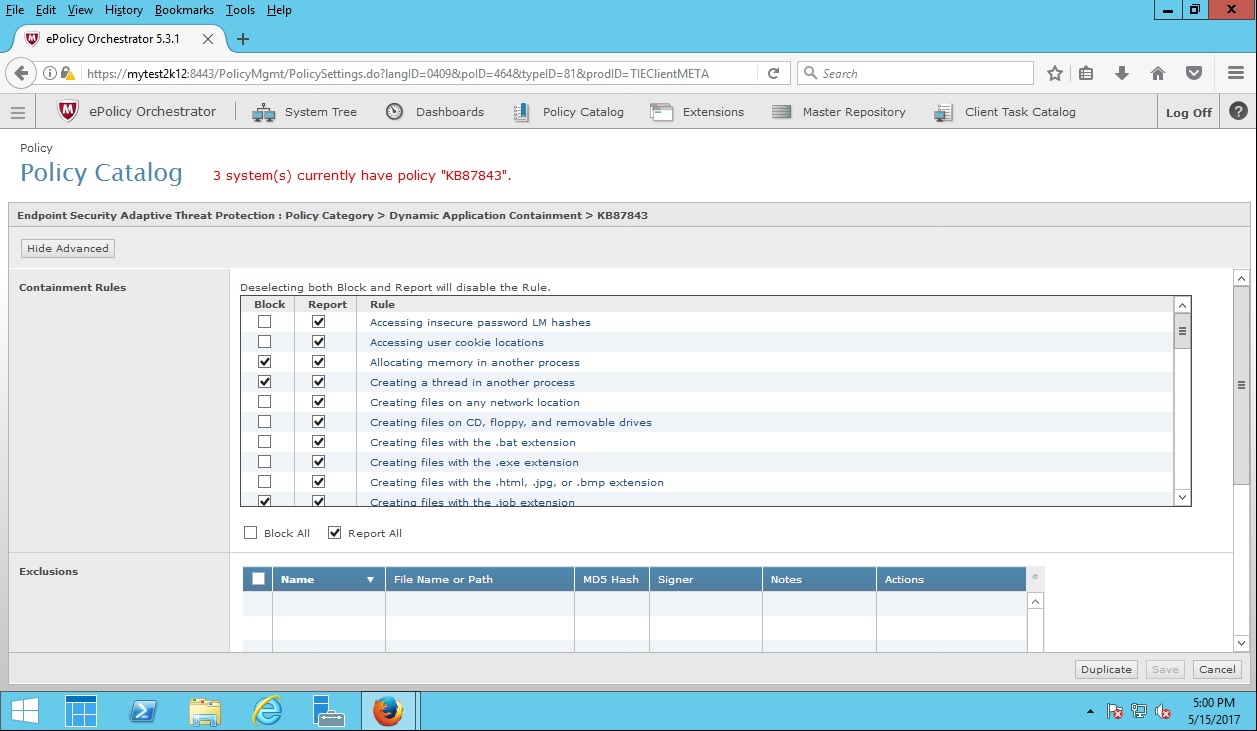
- Configure the following rules in the Adaptive Threat Protection – Dynamic Application Containment policy:
Dynamic Application Containment – Containment Rules
See KB87843 - Dynamic Application Containment rules and best practices, and set the recommended DAC rules to Block as prescribed.
Back to top
ENS DAC rules triggered by Ransom-WannaCry variants
This section provides additional information about observed DAC rules triggered by known WannaCry variants. For processes that other layers of the ENS security stack don't detect, extra rule enablement might not be needed to effectively contain the processes. See KB87843 - Dynamic Application Containment rules and best practices, and set the recommended DAC rules to Block as prescribed.
Rule 1:
Rule Name: Executing any child process
Rule 2:
Rule Name: Accessing user cookie locations
Rule 3:
Rule Name: Creating files with the .html, .jpg, or .bmp extension
Rule 4:
Rule Name: Creating files with the .exe extension
Rule 5:
Rule Name: Modifying users' data folders
Rule 6:
Rule Name: Modifying startup registry locations
Rule 7:
Rule Name: Modifying critical Windows files and registry locations
Rule 8:
Rule Name: Reading or modifying files on any network location
Rule 9:
Rule Name: Modifying files with the .bat extension
Rule 10:
Rule Name: Modifying files with the .vbs extension
Rule 11:
Rule Name: Creating files with the .bat extension
Rule 12:
Rule Name: Reading files commonly targeted by ransomware-class malware
Rule 13:
Rule Name: Creating files on any network location
Rule 14:
Rule Name: Writing to files commonly targeted by ransomware-class malware
Rule 15:
Rule Name: Modifying the hidden attribute bit
Back to top
Advanced Threat Defense (ATD) Content Update Package for WannaCry available in the following builds, or later:
3.6.x – 3.6.2.103.61987 or later
3.8.x package – 3.8.2.170207.59307 or later
3.10.x – 3.10.2.170712.61985 or later
4.0 – Detection included in base install
IPS coverage for WannaCry Ransomware:
Existing signatures:
- 0x43c0b800- NETBIOS-SS: Windows SMBv1 identical MID and FID type confusion vulnerability (CVE-2017-0143)
- 0x43c0b400- NETBIOS-SS: Windows SMB Remote Code Execution Vulnerability (CVE-2017-0144)
- 0x43c0b500- NETBIOS-SS: Windows SMB Remote Code Execution Vulnerability (CVE-2017-0145)
- 0x43c0b300- NETBIOS-SS: Microsoft Windows SMB Out of bound Write Vulnerability (CVE-2017-0146)
- 0x43c0b900- NETBIOS-SS: Windows SMBv1 information disclosure vulnerability (CVE-2017-0147)
Back to top
Frequently Asked Questions about Ransom-WannaCry
Does having Application Control in block mode help prevent the infection?
Yes, because Application Control
blocks any new hash values that aren't in the allow list.
Does a combination of Threat Intelligence Exchange (TIE) and ATD block this threat on Day 0?
TIE and ATD contain several 0-day WannaCry samples. For the samples that are missed, further intelligence is added to the cloud, which picks up subsequent WannaCry variants as 0-day. ATD also releases content updates that are specific to WannaCry. These content updates are available in current builds.
Why are you naming the Access Protection rules generically?
Rule names make no impact on the rule itself and can be named anything you want.
Why doesn't the software key use ‘\’ and not ‘/’?
‘\’ is the correct syntax one should enter, but the managed product modifies the path and replaces ‘\’ with ‘/’.
Why isn't the file extension rule: **\*.wnry?
ENS and VSE use different wildcard syntaxes; so, it's best to use
*.wnry, as both can use this rule properly.
What Regular DAT file is coverage released in?
ENS DAT 2978 or later
VSE DAT 8527 or later