Security Bulletin - Endpoint Security update fixes a configuration editing vulnerability (CVE-2020-7263)
Security Bulletins ID:
SB10314
Last Modified: 2022-05-04 16:53:44 Etc/GMT
Last Modified: 2022-05-04 16:53:44 Etc/GMT
Summary
First Published: March 31, 2020
Recent updates to this article
Article contents:
ENS offers the ability for a local administrator to export the configuration being enforced. The encryption key used is common across multiple versions of ENS, allowing a malicious actor with local administrator rights to export the configuration and decrypt it. The actor can then use a text editor to alter the configuration, including disabling several ENS features. It's possible to then encrypt the modified configuration and ask ENS to import it. This configuration would then be applied, potentially disabling all protection on the system.
The ENS July 2020 Update introduces a new Access Protection rule "Unauthorized execution of EsConfigTool" that's enabled by default. Administrators can disable the rule if they want to run the tool to export or import policies locally. They then need to re-enable the rule after use of the tool.
ENS offers the ability to lock the client interface, and to require a password when exporting and importing configuration. We recommend that both features are enabled. Steps to enable these options are described in the Workaround section below.
CVE-2020-7263 – ENS configuration can be edited by attackers with local administrator permissions
Improper access control vulnerability inESConfigTool.exe in ENS for Windows prior to 10.7.0 July 2020 Update allows a local administrator to alter the ENS configuration up to and including disabling all protection offered by ENS via insecurely implemented encryption of configuration for export and import.
NVD CVE-2020-7263
MITRE 2020-7263
Remediation
Download and Installation Instructions
For instructions to download product updates and hotfixes, see KB56057 - How to download Enterprise product updates and documentation. Review the Release Notes and Installation Guide for instructions on how to install these updates. All documentation is available at our Product Documentation site.
Workaround
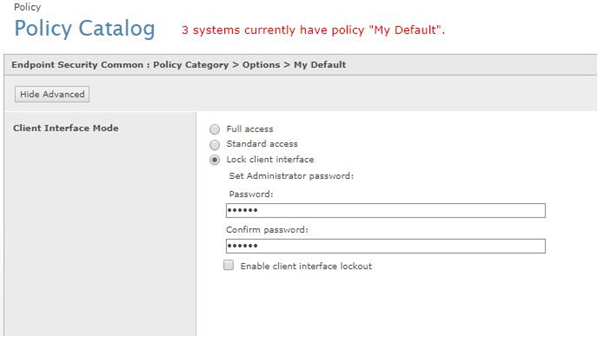
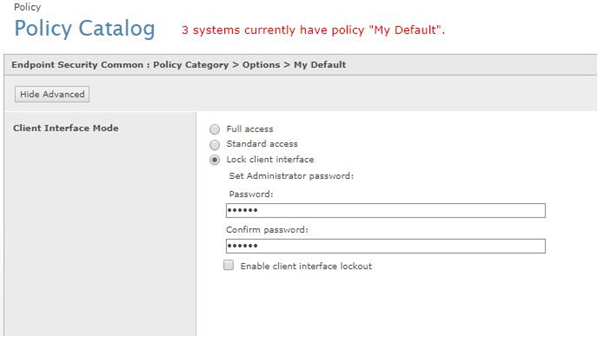
For ENS installations that ePO manages, you can enable "Standard access" or "Lock client Interface" for all your installations centrally. This configuration is done through the Policy Catalog as shown in the image below.
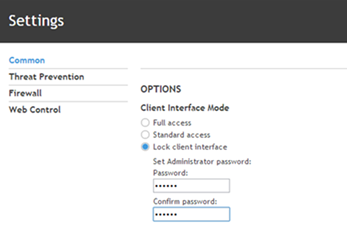
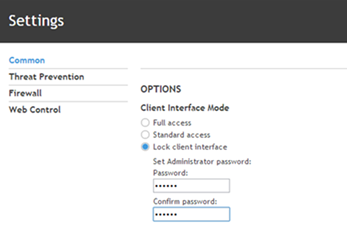
For ENS installations that ePO doesn't manage, you can enable "Standard access" or "Lock client Interface" through the local control User Interface for each installation.
Acknowledgments
We creditDonny Maasland from Fox-IT for reporting this flaw.
Frequently Asked Questions (FAQs)
How do I know if my product is vulnerable?
For Endpoint products:
Use the following instructions for endpoint or client-based products:
Common Vulnerability Scoring System (CVSS) is the result of the National Infrastructure Advisory Council's effort to standardize a system of assessing the criticality of a vulnerability. This system offers an unbiased criticality score between 0 and 10 that customers can use to determine how critical a vulnerability is and plan accordingly. For more information, visit the CVSS website.
When calculating CVSS scores, we adopt a philosophy that fosters consistency and repeatability. Our guiding principle for CVSS scoring is to score the exploit under consideration by itself. We consider only the immediate and direct impact of the exploit under consideration. We don't factor into a score any potential follow-on exploits that might be made possible by the successful exploitation of the issue being scored.
What are the CVSS scoring metrics?
CVE-2020-7263: ENS configuration can be edited by attackers with local administrator permissions
NOTE: The below CVSS version3.1 vector is used to generate this score.
Where can I find a list of all Security Bulletins?
All Security Bulletins are published on our Knowledge Center. Security Bulletins are retired (removed) once a product is both End of Sale and End of Support (End of Life).
How do I report a product vulnerability to you?
If you have information about a security issue or vulnerability with a product, follow the instructions provided in KB95563 - Report a vulnerability.
How do you respond to this and any other reported security flaws?
Our key priority is the security of our customers. If a vulnerability is found within any of our software or services, we work closely with the relevant security software development team to ensure the rapid and effective development of a fix and communication plan.
We only publish Security Bulletins if they include something actionable such as a workaround, mitigation, version update, or hotfix. Otherwise, we would simply be informing the hacker community that our products are a target, putting our customers at greater risk. For products that are updated automatically, a non-actionable Security Bulletin might be published to acknowledge the discoverer.
To view our PSIRT policy, see KB95564 - About PSIRT.
Resources
Disclaimer
The information provided in this Security Bulletin is provided as is without warranty of any kind. We disclaim all warranties, either express or implied, including the warranties of merchantability and fitness for a particular purpose. In no event shall we or our suppliers be liable for any damages whatsoever including direct, indirect, incidental, consequential, loss of business profits, or special damages, even if we or our suppliers have been advised of the possibility of such damages. Some states don't allow the exclusion or limitation of liability for consequential or incidental damages, so the preceding limitation may not apply.
Any future product release dates mentioned in this Security Bulletin are intended to outline our general product direction, and they shouldn't be relied on in making a purchasing decision. The product release dates are for information purposes only, and may not be incorporated into any contract. The product release dates aren't a commitment, promise, or legal obligation to deliver any material, code, or functionality. The development, release, and timing of any features or functionality described for our products remain at our sole discretion and may be changed or canceled at any time.
Recent updates to this article
| Date | Update |
| May 4, 2022 | Updated links. |
| April 25, 2022 | Removed End of Life Endpoint Security (ENS) 10.5.x version. |
| Impact of Vulnerability | Permissions, Privileges, and Access Controls – CWE-264 |
| CVE ID | CVE-2020-7263 |
| Severity Rating | Medium |
| CVSS v3 Base/Temporal Scores: | 6.5 / 5.4 |
| Recommendations | Update to one of the following ENS versions:
|
| Security Bulletin Replacement | None |
| Affected Software |
|
| Location of updated software | Product Downloads site |
To receive email notification when this article is updated, click Subscribe on the right side of the page. You must be logged on to subscribe.
Article contents:
- Vulnerability Description
- Remediation
- Workaround
- Acknowledgments
- Frequently Asked Questions (FAQs)
- Resources
- Disclaimer
ENS offers the ability for a local administrator to export the configuration being enforced. The encryption key used is common across multiple versions of ENS, allowing a malicious actor with local administrator rights to export the configuration and decrypt it. The actor can then use a text editor to alter the configuration, including disabling several ENS features. It's possible to then encrypt the modified configuration and ask ENS to import it. This configuration would then be applied, potentially disabling all protection on the system.
The ENS July 2020 Update introduces a new Access Protection rule "Unauthorized execution of EsConfigTool" that's enabled by default. Administrators can disable the rule if they want to run the tool to export or import policies locally. They then need to re-enable the rule after use of the tool.
ENS offers the ability to lock the client interface, and to require a password when exporting and importing configuration. We recommend that both features are enabled. Steps to enable these options are described in the Workaround section below.
CVE-2020-7263 – ENS configuration can be edited by attackers with local administrator permissions
Improper access control vulnerability in
NVD CVE-2020-7263
MITRE 2020-7263
Remediation
- Customers on earlier ENS 10.7.0 releases: Update to the ENS 10.7.0 July 2020 Update.
- Customers on ENS 10.6.x: Upgrade to the ENS 10.7.0 July 2020 Update or ENS 10.6.1 July 2020 Update.
| Product | Version | Type | Release Date |
| ENS | 10.7.0 July 2020 Update | Update | July 29, 2020 |
| ENS | 10.6.1 July 2020 Update | Update | July 29, 2020 |
Download and Installation Instructions
For instructions to download product updates and hotfixes, see KB56057 - How to download Enterprise product updates and documentation. Review the Release Notes and Installation Guide for instructions on how to install these updates. All documentation is available at our Product Documentation site.
Workaround
For ENS installations that ePO manages, you can enable "Standard access" or "Lock client Interface" for all your installations centrally. This configuration is done through the Policy Catalog as shown in the image below.
For ENS installations that ePO doesn't manage, you can enable "Standard access" or "Lock client Interface" through the local control User Interface for each installation.
Acknowledgments
We credit
Frequently Asked Questions (FAQs)
How do I know if my product is vulnerable?
For Endpoint products:
Use the following instructions for endpoint or client-based products:
- Right-click on the tray shield icon on the Windows taskbar.
- Select Open Console.
- In the console, select Action Menu.
- In the Action Menu, select Product Details. The product version displays.
Common Vulnerability Scoring System (CVSS) is the result of the National Infrastructure Advisory Council's effort to standardize a system of assessing the criticality of a vulnerability. This system offers an unbiased criticality score between 0 and 10 that customers can use to determine how critical a vulnerability is and plan accordingly. For more information, visit the CVSS website.
When calculating CVSS scores, we adopt a philosophy that fosters consistency and repeatability. Our guiding principle for CVSS scoring is to score the exploit under consideration by itself. We consider only the immediate and direct impact of the exploit under consideration. We don't factor into a score any potential follow-on exploits that might be made possible by the successful exploitation of the issue being scored.
What are the CVSS scoring metrics?
CVE-2020-7263: ENS configuration can be edited by attackers with local administrator permissions
| Base Score | 6.5 |
| Attack Vector (AV) | Local (L) |
| Attack Complexity (AC) | Low (L) |
| Privileges Required (PR) | High (H) |
| User Interaction (UI) | Required (R) |
| Scope (S) | Unchanged (U) |
| Confidentiality (C) | High (H) |
| Integrity (I) | High (H) |
| Availability (A) | High (H) |
| Temporal Score (Overall) | 5.4 |
| Exploitability (E) | Proof-of-Concept (P) |
| Remediation Level (RL) | Workaround (W) |
| Report Confidence (RC) | Confirmed (C) |
NOTE: The below CVSS version3.1 vector is used to generate this score.
Where can I find a list of all Security Bulletins?
All Security Bulletins are published on our Knowledge Center. Security Bulletins are retired (removed) once a product is both End of Sale and End of Support (End of Life).
How do I report a product vulnerability to you?
If you have information about a security issue or vulnerability with a product, follow the instructions provided in KB95563 - Report a vulnerability.
How do you respond to this and any other reported security flaws?
Our key priority is the security of our customers. If a vulnerability is found within any of our software or services, we work closely with the relevant security software development team to ensure the rapid and effective development of a fix and communication plan.
We only publish Security Bulletins if they include something actionable such as a workaround, mitigation, version update, or hotfix. Otherwise, we would simply be informing the hacker community that our products are a target, putting our customers at greater risk. For products that are updated automatically, a non-actionable Security Bulletin might be published to acknowledge the discoverer.
To view our PSIRT policy, see KB95564 - About PSIRT.
Resources
To contact Technical Support, go to the Create a Service Request page and log on to the ServicePortal.
- If you are a registered user, type your User ID and Password, and then click Log In.
- If you are not a registered user, click Register and complete the fields to have your password and instructions emailed to you.
Disclaimer
The information provided in this Security Bulletin is provided as is without warranty of any kind. We disclaim all warranties, either express or implied, including the warranties of merchantability and fitness for a particular purpose. In no event shall we or our suppliers be liable for any damages whatsoever including direct, indirect, incidental, consequential, loss of business profits, or special damages, even if we or our suppliers have been advised of the possibility of such damages. Some states don't allow the exclusion or limitation of liability for consequential or incidental damages, so the preceding limitation may not apply.
Any future product release dates mentioned in this Security Bulletin are intended to outline our general product direction, and they shouldn't be relied on in making a purchasing decision. The product release dates are for information purposes only, and may not be incorporated into any contract. The product release dates aren't a commitment, promise, or legal obligation to deliver any material, code, or functionality. The development, release, and timing of any features or functionality described for our products remain at our sole discretion and may be changed or canceled at any time.








